Triggers
- A successful login has occurred to an account with sign-on attributes (such as location, device, etc.) that are unusual for the account.
Possible Root Causes
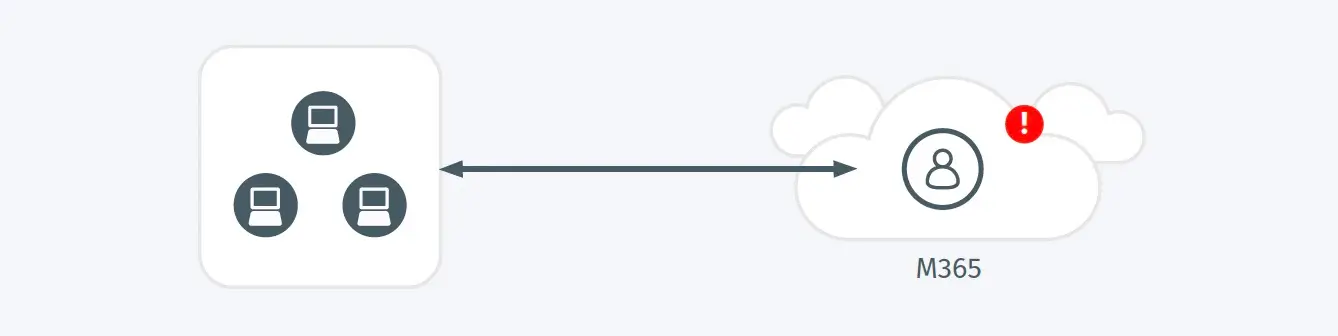
- An adversary has stolen a valid account and is using it as part of an attack.
- A user has moved and performed a full refresh of their devices and performed login activities across these devices with new sign-on attributes.
Business Impact
- Adversaries frequently bypass security controls through the malicious, unauthorized use of valid credentials.
- The compromise of a valid account may lead to the loss of confidentiality and integrity of any data and services that account may access, and it may be used in service of additional lateral movement or attacks against other internal users.
Steps to Verify
- Investigate irregularities associated with these login events for indications of compromise.
- Validate the login activities have been performed in accordance with organizational MFA policies, enforcing re-login with MFA if required.